Ten Entry-Level Jobs in Cybersecurity

Today, most people have a general idea of what cybersecurity is. The definition is practically spelled out in the name — and requires tech-savvy professionals who work to keep businesses (and their data) safe from online threats.
But let’s go beyond the basic definition for a second. Do you actually know the nitty-gritty tasks that professionals in the cybersecurity industry take on each day? Could you name a few specific entry-level cybersecurity jobs?
If you’ve thought about building a cybersecurity career and want to know where your professional journey might take you, it will probably help to get some background. In this article, we’ll shed light on the industry, its job prospects, and which positions are open to talented, entry-level candidates.
Let’s get started!
What is Cybersecurity, and Why Should I Care?
Cybersecurity is a broad term that refers to all of the processes, technologies, and individuals that collectively protect organizations from digital attacks. Among other responsibilities, cybersecurity professionals install and manage sophisticated security software, search for vulnerabilities within an organization’s digital systems, and create protocols to protect companies, consumers, and information from malicious actors.
Successful cybersecurity teams continually strive to secure networks, proprietary applications, and systems against online threats, creating multiple layers of protection across networks, computers, and sensitive data. As attackers become ever more innovative, it falls to these information security professionals to prevent malicious players from accessing, changing, or destroying sensitive data.
With so much of our daily interactions being performed online, the work cybersecurity professionals do is crucial, especially given the threat hackers pose to businesses today. Even a single digital breach can result in massive financial loss if hackers choose to steal or reveal corporate information, customer data, bank information, or critical business intelligence.
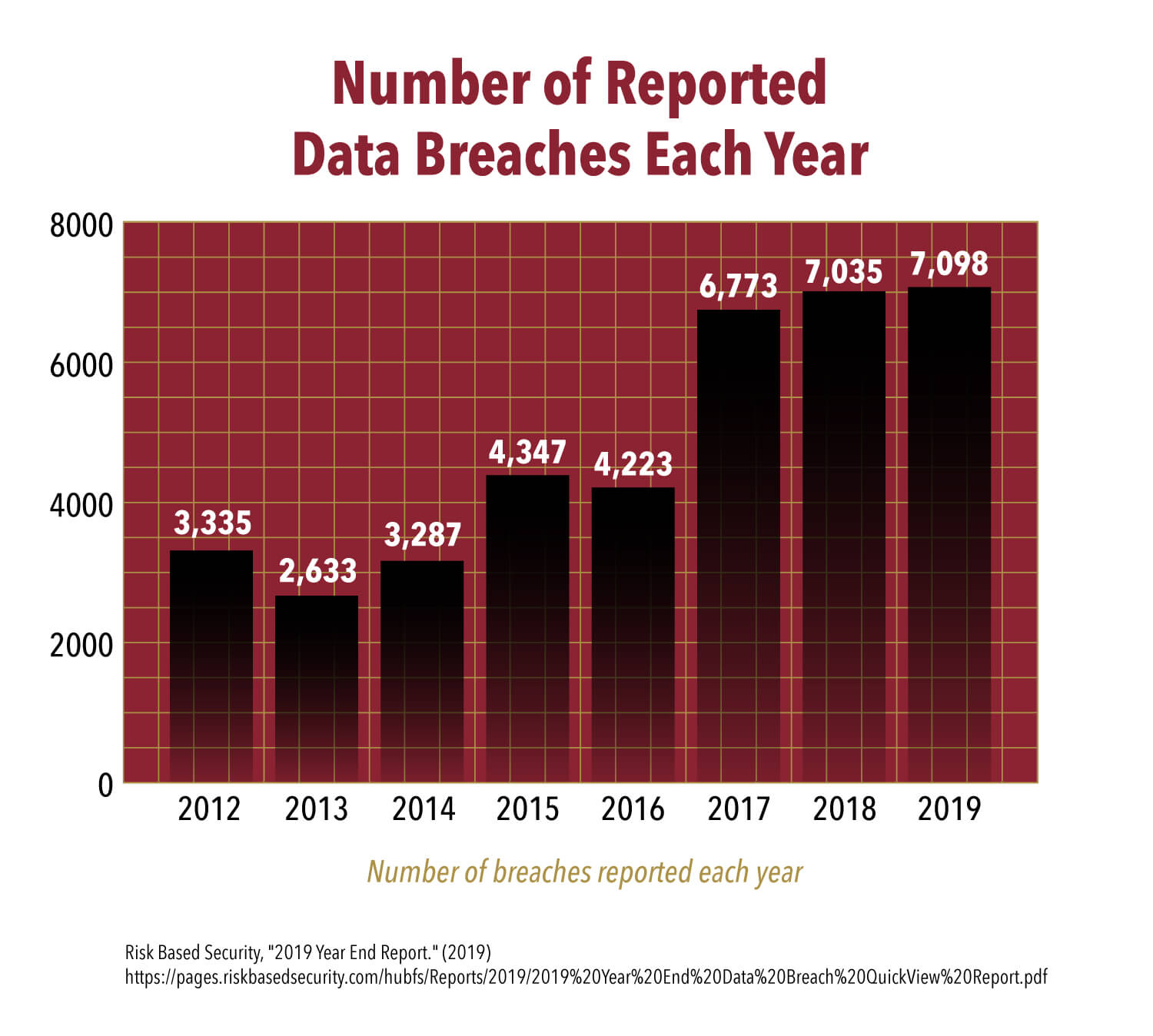
According to RiskBased Security’s most recent Year-End Data Breach QuickView report, 7,098 known breaches exposed 15.1 billion records in 2019. The number of exposed records has increased an incredible 284 percent since 2018 and a still-significant 91 percent since 2017.
Unsurprisingly, the increased risk of digital vulnerability has prompted a parallel expansion of the cybersecurity industry. The global cybersecurity market was valued at $161.07 billion in 2019 and is expected to top $363.05 billion by 2025.
This fast-paced expansion has led to an unprecedented surge in demand for talented cybersecurity professionals. Currently, the need for talent far outstrips the available supply of qualified candidates.
A 2019 report by (ISC)2 noted that the cybersecurity workforce gap is nearly 500,000 in the United States alone. That talent pool would need to grow by 62 percent to meet the current demand posed by American businesses — an untenable task.
To boot, 65 percent of organizations surveyed in (ISC)2’s report claims to have a severe staff shortage when it comes to cybersecurity. Representatives at these businesses claim that the lack of experienced personnel is even more concerning than the inadequacy of available resources. More than half of cybersecurity professionals state that their organization is at “moderate or extreme risk” due to persistent staff shortages.
While the talent shortage poses a clear and pressing problem for businesses, on the flip side, the intense need also creates a fantastic career opportunity for aspiring cybersecurity professionals.
Recent reporting from TechRepublic indicates that major companies such as Apple, General Motors, Capital One, and Cisco have all begun hiring cybersecurity professionals in droves. The same reporter surmises that the industries at higher risk of cyberattacks — healthcare, education, government, e.g., — will also experience a skyrocketing in cybersecurity jobs in upcoming years.
Ten Entry-Level Cybersecurity Jobs
Below, we dive into ten of the best entry-level cybersecurity gigs on the market. Each role has been selected for its unique blend of job responsibilities, top job prospects, and opportunities for future growth.

1. Security Analyst/Manager
Security analysts play a pivotal role in keeping business intelligence safe from malicious agents that seek to modify, view, or destroy data. The analyst works to identify and correct flaws in existing security systems, often working with multiple departments to develop new processes.
Analysts work directly with collected data to spot suspicious activity in databases, servers, networks, or other proprietary software. Once a breach occurs, analysts lead efforts to mitigate the damage and prevent future attacks.
Security analysis is considered an entry-level cybersecurity job, often requiring a bachelor’s degree in computer science or a related field. Most companies seek analysts with one to five years of on-the-job experience in systems administration.
Analysts are often promoted to managers, which take on a more senior role by helping to direct a team of subordinate analysts on day-to-day security tasks. Most managerial positions require at least five years of specific experience in security analysis.
Top industries for analysts include financial services, government, health care, manufacturing, and nonprofit companies.
2. Security Specialist
Security specialists are tasked with maintaining an organization’s automated security systems and employee identification databases.
These professionals are responsible for protecting company data, ensuring the digital safety of end-users, assisting senior management with onboarding new employees securely, and interfacing with leadership to form guidelines around company policy and network use.
As an intermediary role, most security specialist positions require five to seven years of relevant experience. Industries that commonly employ security specialists include aerospace, defense contracting, energy and utilities, financial services, government, and higher education. Security specialists also tend to work in industries such as tech and finance.
Companies often promote security specialists to more senior roles such as team leaders or cross-departmental communicators.
3. Incident Responder
Incident responders use digital forensics to investigate breaches and other security events.
Everyday responsibilities of the role may include assessing systems for risk, automation testing, and conducting system analysis to identify threats and react to potential breaches.
This is a high-pressure role that requires a keen eye for detail and the ability to communicate productively across different departments. Incident responders are required to create comprehensive reports for management and communicate with those from non-technical backgrounds.
Most incident responder roles require two to three years of experience in information security or cyber forensics. Network or system administrator positions often feed into this position.
Incident responders work in all kinds of sectors including finance, nonprofit, tech, and aerospace.
4. Cryptographer
Cryptographers have one of the most interesting cybersecurity jobs on this list. They use specialized algorithms and ciphers to encrypt sensitive data to develop security systems. These professionals protect data from being copied, modified, destroyed, or intercepted by unauthorized agents.
Cryptographers typically have a background in statistics, as their role requires them to develop mathematical models that are capable of analyzing emerging security threats. Cryptography positions further require a comprehensive theoretical understanding of how cryptographic theories can apply real-world solutions to IT systems.
Most roles require a bachelor’s degree in mathematics, computer science, or computer engineering. Alternatively, the position may require five or more years of relevant experience in systems administration, auditing, or data encryption.
Cryptographers work in industries spanning the gamut from government and technology to finance and health care. Any industry that requires protecting sensitive client and business data may have a use for cryptographers.
5. Security Architect
As the name suggests, security architects help to build enterprise-level information systems that meet robust security requirements. Key responsibilities include security planning and testing, as well as designing and implementing new security protocols.
Architects are required to have a broad level mastery of the software and systems that a company employs to keep sensitive data secure. These professionals need to possess a thorough understanding of network security, hardware configuration, network protocols, and the specific procedures in place at their company.
As an intermediate role, security architects are usually required to have five to ten years of relevant experience, with at least three years explicitly dedicated to security. Security architects are often promoted to managerial roles in network security because they already have a broad-level overview of the systems.
Industries that employ security architects include defense, government, financial companies, and aerospace.
6. Security Auditor
Auditing — it’s a term that doesn’t bring most people joy. But for cybersecurity professionals, this field can offer tremendous opportunities for growth. Security auditors perform the vital task of verifying security procedures, preserving system safety, and compiling reports.
This position requires steadfast attention to detail. Auditors strive to identify potential vulnerabilities and flaws within internal systems before they become a problem. The role requires regular penetration testing, documentation, and communication between departments.
Security auditors are most often promoted from within a company’s cybersecurity department and boast three to five years of security-related or systems administration experience. Entry-level positions for new computer science graduates also exist in government and nonprofit industries.
Auditors often proceed to more senior roles in security architecture or management.
7. Forensic Expert
Forensic experts are responsible for retrieving data, analyzing network traces, and collecting evidence from diverse computer systems. When devices are physically or digitally damaged, forensic experts help to conduct investigations concerning the party or parties responsible.
Forensics specialists may also be required to recover information, reconstruct damaged hardware, and ensure that all work is completed in compliance with federal law.
While forensics experts most often work in the crime investigation sector, many work in private industries like healthcare, defense contracting, and tech. Entry-level positions require at least one to three years of relevant experience in forensics, while senior roles require five or more.
Forensics experts can be promoted to supervisory roles overseeing regional labs or managing quality assurance guidelines. Some of these professionals move on to college teaching roles after receiving an advanced degree.
8. Penetration Tester
A penetration tester, or pentester, is responsible for identifying existing security issues within a company’s information infrastructure. Pen testers are also referred to as “ethical hackers” or security consultants. That also makes this one of the more trendy cybersecurity jobs out there.
Pen testers must perform wireless assessments of wifi systems, physical assessments of the underlying hardware, social engineering tests, and phishing assessments for end-users within a company.
Low-level penetration testing roles require one to four years of experience in related fields such as systems administration, network administration, or network engineering. After receiving more specialized qualifications, many pentesters can become information technology managers or systems architects.
Industries like banking, health care, retail — or, practically speaking, any sector that strives to secure client data — may hire pentesters to improve their systems.
9. Security Engineer
Security engineers are responsible for designing, implementing, and monitoring security measures to protect enterprise-level applications and networks. Engineers must be able to troubleshoot infrastructure devices, develop novel solutions to mitigate risk, and communicate developing problems with senior managers.
Engineers typically need one to five years of related IT experience in network administration or systems analysis. The most common employment industries include tech, finance, health care, defense, government, and higher education.
Security engineers are often promoted to managerial roles as they develop a deeper understanding of the proprietary security systems that their business relies on.
10. Source Code Auditor
Source code auditors work directly with a company’s codebase to identify potential bugs, weaknesses, and syntax errors. Auditors may regularly perform penetration tests, review company protocols, and implement fixes that optimize code behavior.
These auditors work closely with both development teams and non-technical departments to communicate new findings. If a data breach occurs, an auditor may be called to work with legal teams or investigate how the leak occurred.
These auditors may be contracted for a short duration by the company or may have a more permanent role. As an entry-level role, most source code auditors are required to have an undergraduate degree in information technology or computer science.
Source code auditors work in virtually every industry, yet most often work with software companies, SaaS (Software as a Service) companies, financial institutions, or online businesses. These professionals are often promoted to specialized penetration testing or systems analysis roles.
Training to Get a Job in Cybersecurity
Inspired to start exploring your career options? We have good news for you. Regardless of your situation, schedule, or learning preferences, you can absolutely find an educational avenue that suits you. In this section, we’ll cover a few of the most popular routes into the industry — but don’t be afraid to try a combination or explore other training options too!
Let’s dive in.
College
If you’re looking for an educational path that provides comprehensive training in the theoretical and practical aspects of cybersecurity, you should probably consider enrolling in an undergraduate program. Beyond simple instruction, these four-year programs offer ample opportunity for networking, internship experience, and portfolio-padding projects.
It is worth noting that attending college is one of the more expensive routes aspiring cybersecurity professionals can take — and that enrollment typically requires a full-time commitment for four years. However, if you have the time and resources to commit, an undergraduate degree is undoubtedly worth pursuing.
If you choose to go this route, you should opt for a major that can provide you with a robust background in programming, statistics, ethics, and computer forensics.
Want more information on how to pursue a cybersecurity career through university training? Check out these resources:
- What to Expect in an Online Cybersecurity Degree Program — U.S. News
- Top 15 Mistakes to Avoid in Choosing a College — FastWeb
- All About College Hackathons — Major League Hacking
Boot Camps
Have you already obtained your undergraduate degree in a discipline unrelated to cybersecurity? Do you lack the time, resources, or inclination to commit to a four-year program? Don’t worry — you still have options.
College degrees are not the end-all-be-all of cybersecurity training. Today, many professionals access their instruction via intensive cybersecurity boot camps that are specifically designed to equip students with job-ready skills.
Most boot camps last anywhere between three and six months. These courses take place online or in-person, and many also offer part-time programs with enough flexibility to allow students with preexisting work and family commitments to learn on the side. These specialized programs often cover subjects such as risk assessment, vulnerability detection, ethical hacking, full stack development, and system administration.
Interested in exploring what a boot camp has to offer? Look through these linked resources:
- What Are Cyber Security Boot Camps? — Webopedia
- Are Bootcamps Worth It? What Employers Really Think — Indeed
- Opinion: Should I Keep My Job While Completing a Bootcamp? — LE Wagon
Independent Learning
Though boot camps and college degrees are worthwhile investments, not everyone can commit the time or money needed to complete a formal program. Instead, some professionals start with self-directed study to obtain the skills they need.
With a killer portfolio and open-source projects, you can land entry-level cybersecurity jobs without ever completing a formal program. However, it is worth stating that this educational route is a difficult one that requires tremendous discipline and self-motivation. Those who opt to learn on their own will need to be seriously dedicated and passionate enough to get their foot in the door.
Alternatively, you may want to consider using online resources to build your foundational knowledge of the industry before enrolling in a structured program.
Consider these online resources to tune up your cybersecurity knowledge:
- Top Ten Cybersecurity Books — InfoSecurity Magazine
- The Best Cybersecurity Certifications to Boost Your Career — New Horizons
- Five Ways to Immerse Yourself in the Cybersecurity Field — Security Boulevard
Will You Pursue a Career in Cybersecurity?
If you’ve made it this far, you probably have the passion and drive to hack it in cybersecurity. But where will you go — and what will you need to do to achieve your professional goals?
Take some time to go back through the above list of cybersecurity jobs, noting any that seem particularly interesting or worth considering. As you do so, think: Why are you attracted to those roles in particular? Are you a natural investigator who gravitates towards digital forensics work? Do you prefer being taking up a more proactively protective stance as a security architect or engineer?
Once you’ve established your general professional direction, you can start planning your educational journey. Take some time to consider your options! Four-year degrees, boot camps, and even self-study can equip you with the skills you need to succeed in cybersecurity jobs.
You can pursue a rewarding career in cybersecurity — but will you?

 Live Chat
Live Chat